SecAppDev 2026 lecture details
Secure by Design — A Design Lens on Real Breaches
Real breaches, analysed not for how they were exploited but for why they were exploitable. Each reveals a design omission that Secure by Design thinking could have caught — and a lesson you can apply to your own systems.
Wednesday June 3rd, 09:00 - 10:30
Room Lemaire
Add to calendar (ICS) Add to Google calendarAbstract
When a breach happens, post-mortems focus on what was exploited. But there's a more uncomfortable question: why was it exploitable at all? In most cases the answer isn't a missing patch — it's a design question nobody asked.
We take real, high-profile cases and do a different kind of analysis, looking past exploit mechanics to ask: what design omission made this structurally possible? The vulnerability wasn't introduced. It was never designed out. You'll leave with a new way of reading breach reports and new questions to bring back to your own systems.
Key takeaway
Breaches have root causes deeper than the exploit. Learn to trace them back to design omissions
Content level
Deep-dive
Target audience
Developers, architects, and security practitioners who reason about incidents at the design level.
Prerequisites
Some familiarity with Secure by Design thinking is helpful — but curious, experienced practitioners will find their footing quickly.

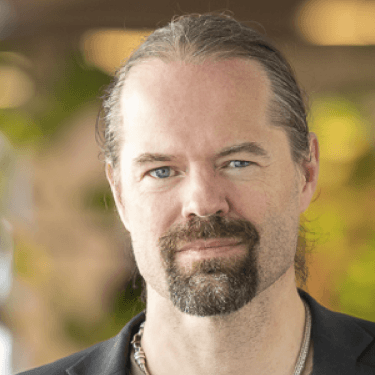
Dan Bergh Johnsson
AI Head, Omegapoint
Expertise: High quality system development and security, with side-dish of Agile and AI
Related lectures
Secure by Design — Ideas and Techniques
Introductory lecture by Dan Bergh Johnsson and Daniel Deogun in room West Wing
Monday June 1st,
11:00 - 12:30
Also available as a recorded session on
Tuesday June 2nd,
14:00 - 15:30
Security is a design concern, not just an implementation concern. This session shows how domain modelling, type design, and boundary thinking can structurally eliminate entire classes of vulnerability - before attackers ever get a chance.
Key takeaway: Security is a quality aspect of software - like maintainability or correctness. Teams that design for quality get security as an emergent benefit
What's New in ASVS v5
Advanced lecture by Eden Sofia Yardeni in room West Wing
Tuesday June 2nd, 14:00 - 15:30
A practical session for security practitioners already familiar with ASVS, covering what changed in v5, how to apply it in code review, how it can be used alongside other AppSec tools, and common pitfalls / best practices.
Key takeaway: Coding standards are even more relevant in an age where LLMs are writing most code, making ASVS an increasingly useful resource.
Achieving Risk-based and Effective Security Testing
Deep-dive lecture by Ruben De Visscher in room West Wing
Monday June 1st, 14:00 - 15:30
This talk discusses how to achieve a risk-based and effective security testing strategy by taking ownership of what and how to test instead of relying on limited built-in checkers of off-the-shelf security scanning tools.
Key takeaway: Take ownership of your security testing strategy to improve coverage and efficiency, do not let tool vendors create a sub-optimal strategy for you.